🧰 Tool Stack Selection Guide¶
Balancing Openness, Privacy, and Competitiveness
We choose tools that enhance our ability to build privacy-first products — without compromising on quality, velocity, or innovation.
🎯 Purpose¶
This guide defines how Brax Technologies selects, evaluates, and approves its engineering and operations tools. Our mission is to use technology that enhances our ability to build privacy-first products — without compromising on quality, velocity, or innovation.
We acknowledge that not every domain has the same privacy expectations: our core systems (engineering, devices, users) demand full sovereignty, while business operations sometimes rely on external, cloud-based ecosystems.
📍 Guiding Principles¶
🔒 Privacy and Control First
- We prefer tools that let us own our data and control our environment.
- Open-source and self-hosted tools are the default choice whenever feasible.
- The key question: "Who controls the data, and what is its potential exposure risk?"
⚖️ Pragmatism and Efficiency
- We make data-driven, context-aware decisions.
- Some workflows (marketing, recruiting) operate in the public domain — cloud tools acceptable when managed with care.
- We minimize data sharing and retain the right to exit or migrate if vendors’ privacy practices change.
📝 Transparency and Review
- Every major tool adoption undergoes a lightweight internal review covering technical, privacy, and sustainability considerations.
- Decisions are documented with rationale, risk level, and mitigation steps.
- We maintain a living inventory of our stack and re-evaluate dependencies regularly.
✅ Tool Selection Criteria¶
When evaluating a new tool or platform, we consider:
| Category | Key Questions | Preferred Approach |
|---|---|---|
| 📦 Data Ownership | Who stores and processes the data? | Self-hosted or private cloud preferred |
| 🔒 Privacy Impact | What data is collected and retained? | Minimal, anonymized, auditable |
| 🔐 Security | Does it support encryption, MFA, SSO, access controls? | Mandatory for sensitive systems |
| 📜 Open Source | Is it auditable? What’s the license? | Prefer open-source with active community |
| 🔓 Vendor Lock-In | How easily can we migrate away? | Open standards and exportable data |
| 🚀 Performance & Scale | Does it fit our growth model? | Scalable, maintainable |
| 🤖 AI Integration | Does it expose internal data? | Only if privacy-respecting or self-hosted |
| 🏢 Business Context | Is the data already public or non-sensitive? | Cloud acceptable under control policies |
🌐 Open Source vs. Cloud Tools¶
✅ Open Source (Default)
- Full transparency into code and data flows.
- Customizable and aligned with our mission.
- Ideal for core engineering systems: CI/CD, firmware builds, device management, analytics, and AI pipelines.
Examples: GitLab (self-hosted), Matrix/Element, Nextcloud, Grafana, Hugging Face local inference servers.
⚠️ Cloud Tools (Controlled Use)
Some business operations benefit from managed cloud platforms — provided we manage exposure and contractual controls.
We adopt cloud tools when they:
- Do not process user or device data, or
- Handle already public or non-sensitive information (e.g., marketing content, candidate CVs, CRM data), and
- Offer data export and deletion capabilities.
⚖️ Pragmatic Compromises for Business Operations¶
At Brax, compromise never means carelessness — it means we understand the data’s context and sensitivity. We may use trusted cloud tools for specific business areas where privacy risk is inherent but manageable.
| Domain | Typical Data | Acceptable Cloud Use | Controls |
|---|---|---|---|
| 📢 Marketing & Advertising | Website traffic, campaign metrics, lead data | Analytics, SEO tools, ad networks | Use privacy filters, anonymization, consent-based tracking |
| 💼 Sales & CRM | Contact info, business communication | HubSpot, Pipedrive, Salesforce | Limit personal data; enforce GDPR compliance |
| 💳 Payment Processing | Billing, transaction metadata | Stripe, PayPal | Tokenized; Brax does not store card data |
| 📝 Recruiting & HR | Applicant resumes, job posts | Greenhouse, Lever | Store only necessary personal data; delete post-hire cycle |
| 📱 Social Media & PR | Public-facing content | LinkedIn, X, YouTube | No internal or customer data sharing |
| ✉️ Email & Collaboration | Internal discussions, outreach | ProtonMail, Google Workspace (restricted) | Segregate sensitive communication via secure channels |
Key Rule: Cloud tools may be used only where the data is already exposed by nature or is non-sensitive. Internal product telemetry, user data, and system logs remain strictly under Brax’s control.
🤖 Artificial Intelligence and Privacy¶
AI adds tremendous capability — but also privacy risk. Our stance remains: use AI, but guard the data.
📜 AI Usage Principles¶
✅ Acceptable AI Uses¶
- 💻 Local AI coding assistants
- 📊 Internal analytics on anonymized telemetry
- ✍️ Marketing content generation (with non-user data)
- 🤖 Automated documentation and testing tools
🔄 Decision Process¶
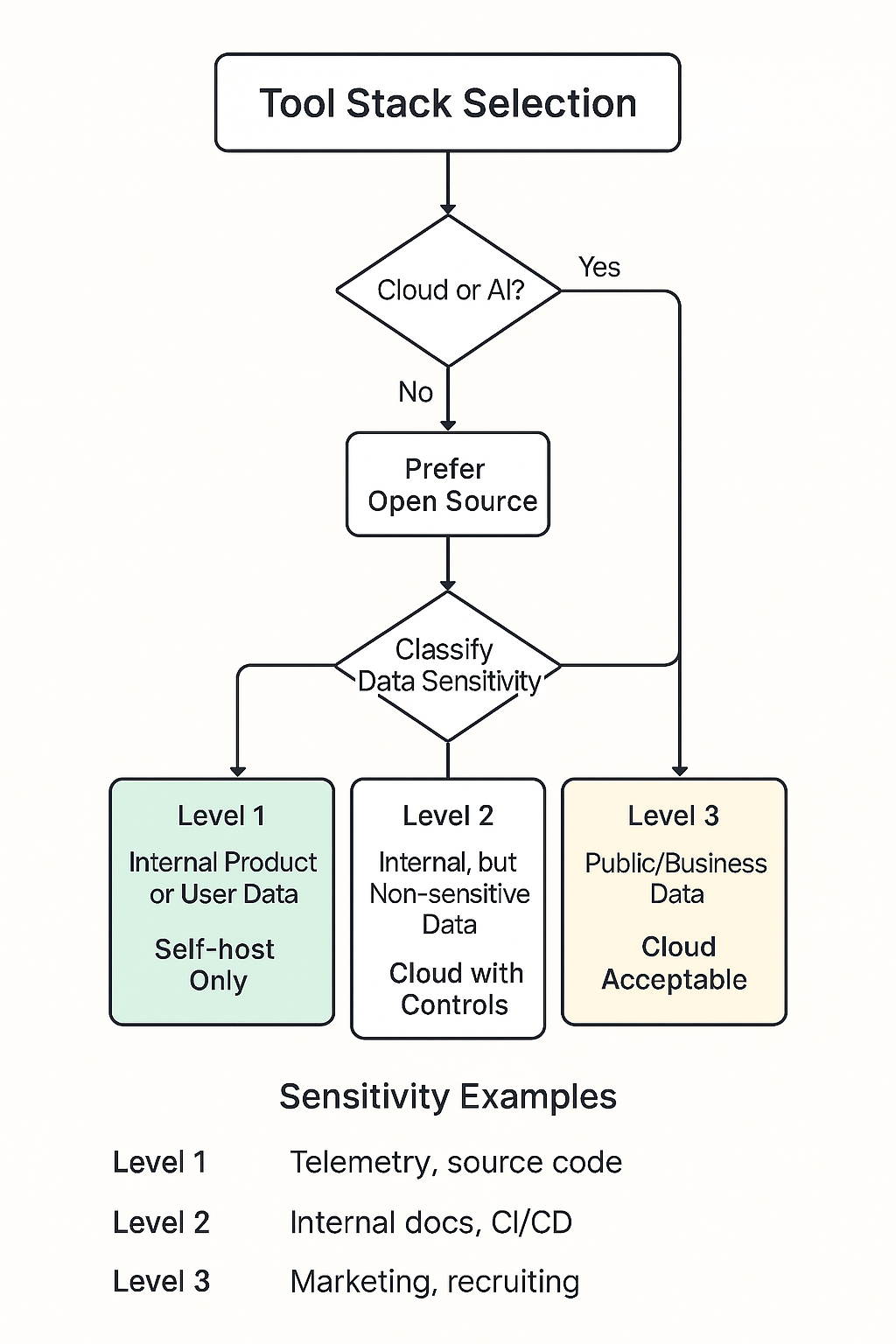
- Propose: Engineer or team identifies a need.
- Evaluate: Assess open-source and cloud alternatives using the criteria above.
- Classify Data Sensitivity:
- Level 1: User or device data → Self-host only
- Level 2: Internal but non-sensitive → Cloud with contract controls
- Level 3: Public/business data → Cloud acceptable
- Review: Privacy and security teams approve or reject.
- Trial: Deploy small-scale pilot.
- Document: Record decision and rationale.
- Reassess: Reevaluate every 6–12 months.
🎯 Conclusion¶
Brax Technologies operates in the real world — where privacy, performance, and business needs must coexist. We protect user trust at all costs while staying agile and competitive through smart tool choices.
🔒 Privacy is our principle. ⚖️ Pragmatism is our practice. 🤝 Trust is our advantage.